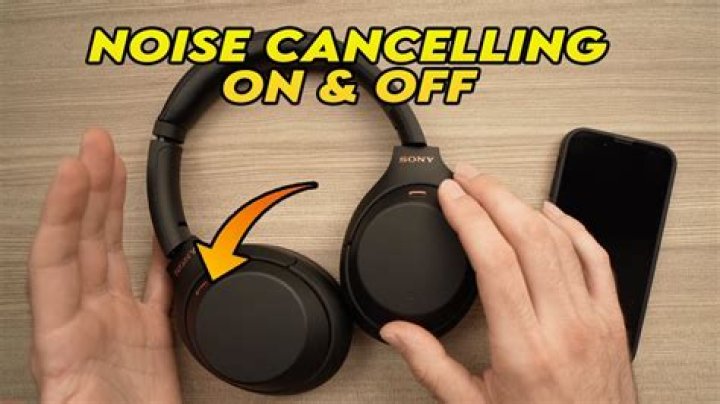
DOD PKI client certificates include 1 identity, 1 email signature, and 1 email encryption certificate, and may be obtained from the DoD free of charge. Keeping this in consideration, what certificates are contained on the CAC?
Depending on the owner, the CAC contains one or three PKI certificates. If the CAC is used for identification purposes only, an ID certificate is all that is needed. However, in order to access a computer, sign a document, or encrypt email, signature and encryption certificates are also required.
Subsequently, question is, which organization issues the directives concerning the dissemination of information? Department of defense issues the directives concerning the dissemination of information regarding intelligence sources, methods, or activities.
People also ask, what is a sensitive compartmented information program quizlet?
A program that segregates various type of classified information into distinct compartments for added protection and dissemination for distribution control.
Which is a rule for removable media?
What is a rule for removable media, other portable electronic devices (PEDs), and mobile computing devices to protect Government systems? Do not use any personally owned/non-organizational removable media on your organization's systems. You just studied 2 terms!
Related Question Answers
What is an indication that malicious code is running on your system DoD?
What is a possible indication of a malicious code attack in progress? A pop-up window that flashes and warns that your computer is infected with a virus. What is the best practice while traveling with mobile computing device?
What is a best practice while traveling with mobile computing devices? Maintain possession of your laptop and other government-furnished equipment (GFE) at all times. What is the best way to protect your CAC?
To protect the information on your CAC, you should never tell anyone your PIN or write it down where it can be easily found. Your PIN should be kept secure at all times, just like your Social Security Number. When should a security badge be visible?
When is it appropriate to have your security badge visible within a Sensitive Compartmented Information Facility? It is appropriate to have your security badge visible within a Sensitive Compartmented Information Facility (SCIF) At all times when in the facility. This answer has been confirmed as correct and helpful. How do I get DoD recipients encryption certificates?
Use the link to go to the DOD White Pages (you will need your CAC to log on to the site). This site contains email certificates of everyone in the DoD. b. If you know the recipients email, then just type the email address and nothing else. Can I use my CAC card to get on base?
Your CAC can be used by you to enter any military base which has open facilities for military personnel. Some military facilities are Restricted Areas in their entirety. They are generally mission-specific facilities, not full-service military bases. What is the difference between CAC and PIV cards?
A common access card (CAC) includes a picture used for identification and can also be used as a smart card. While not included in the answers, a personal identity verification (PIV) card also includes a picture and can be used as a smart card. What is an indication that malicious code is running on your system 2021?
What is a possible indication of a malicious code attack in progress? A pop-up window that flashes and warns that your computer is infected with a virus. Do you need a clearance to get a CAC?
A CAC is the Department of Defense Personal Identity Verification (PIV) card required under Homeland Security Presidential Directive (HSPD) 12. Conversely, if you have a security clearance, you can almost guarantee the need for a CAC (or your agency's equivalent). What does the W on my CAC card mean?
Changes to the Front of the CAC. Beginning in July 2015, all Common Access Cards (CACs) will be issued with an affiliation color code in a white circle under the expiration date, including "W" for white, "G" for green, and "B" for blue. What certificates are contained on the Common Access Card CAC cyber awareness?
Card Body Information - Public Key Infrastructure (PKI) certificates that enable cardholders to "sign" documents digitally, encrypt and decrypt emails, and establish secure online network connections.
- Two digital fingerprints.
- Digital photo.
- Personal Identity Verification (PIV) certificate.
- Organizational affiliation.
- Agency.
Is a CAC a military ID?
The CAC, a "smart" card about the size of a credit card, is
the standard identification for active duty uniformed Service personnel, Selected Reserve, DoD civilian employees, and eligible contractor personnel.
| Color Coding |
| Blue Bar: Non-U.S. Citizen | Green Bar: Contractors | White: All Remaining Personnel |
Which of the following is the best example of protected health information?
Health information such as diagnoses, treatment information, medical test results, and prescription information are considered protected health information under HIPAA, as are national identification numbers and demographic information such as birth dates, gender, ethnicity, and contact and emergency contact What describes how sensitive compartmented information?
Sensitive Compartmented Information (SCI) is information about certain intelligence sources and methods and can include information pertaining to sensitive collection systems, analytical processing, and targeting, or which is derived from it. What describes how sensitive compartmented?
SCI is a classification label indicating that items or information is sensitive and part of a specific program or department. SCI is a classification based on intelligence information that requires appropriate protection with a specific control system. What are some examples of malicious code cyber awareness?
Malicious code includes viruses, trojan horses, worms, macros, and scripts. They can damage or compromise digital files, erase your hard drive and/or allow hackers access to your PC or mobile from a remote location. What must you ensure before transmitting personally identifiable information?
What must you ensure before transmitting Personally Identifiable Information (PII) or Protected Health Information (PHI) via e-mail? Transmissions must be between Government e-mail accounts and must be encrypted and digitally signed when possible. What advantages do insider threats have over others quizlet?
What advantages do "insider threats" have over others that allows them to be able to do extraordinary damage to their organizations? They are trusted and have authorized access to Government information systems. What is a sensitive compartmented information program cyber awareness?
What decribes a Sensitive Compartmented Information (SCI) program? A program that segregates various type of classified information into distinct compartments for added protection and dissemination for distribution control. Which of the following can an unauthorized disclosure of information classified as confidential reasonably be expected to cause?
Unauthorized disclosure of Top Secret information could reasonably be expected to cause exceptionally grave damage to our national security. Unauthorized disclosure of Confidential information could reasonably be expected to cause damage to our national security. Which may be a security issue with compressed URLs?
Shortened URLs, such as those from bit.ly and goo.gl make it easy to type in a web address quickly, but difficult to determine where the web browser will actually take you. Criminals will use shortened URLs to direct victims to phishing sites or initiate a download of malicious software on to your device. What is the best description of two factor authentication cyber awareness?
Two-factor authentication (2FA) is a security system that requires two separate, distinct forms of identification in order to access something. The first factor is a password and the second commonly includes a text with a code sent to your smartphone, or biometrics using your fingerprint, face, or retina. What is the best way to protect your Common Access Card cyber awareness?
What is the best way to protect your Common Access Card (CAC) or Personal Identify Verification (PIV) card? Maintain possession of it at all times. What is the risk associated with removable media?
The use of removable media for delivering malware is dangerous because it sneaks the malware past the security solutions deployed at the organization's network perimeter. Unless an organization has an endpoint security solution in place, it may not detect the attack until it is too late. What is a proper response if spillage occurs quizlet?
What is a proper response if spillage occurs? Immediately notify your security POC. A user writes down details from a report stored on a classified system marked as Secret and uses those details to draft an unclassified briefing on an unclassified system without authorization. What should the participants in this conversation involving SCI differently?
what should the participants in the conversation involving SCI do differently? The participants in this conversation involving SCI do directly should physically assess that everyone within listening distance is cleared and has a need-to-know for the information being [ discussed. ] What are some potential insider threat indicators?
What are some potential insider threat indicators? Difficult life circumstances such as substance abuse, divided loyalty or allegiance to the U.S., and extreme, persistent interpersonal difficulties. 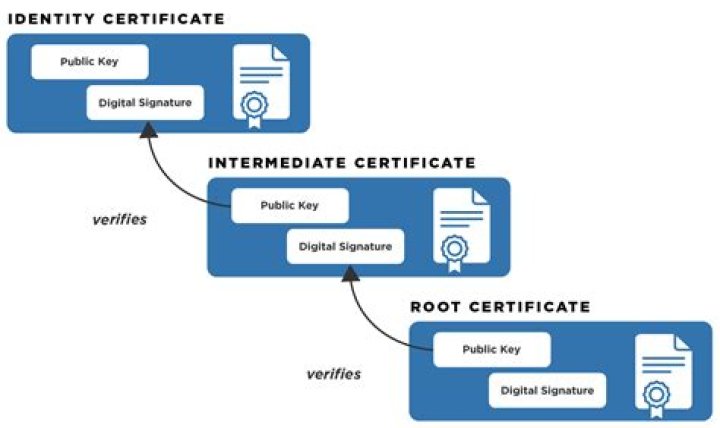
 Olivia Norman
Olivia Norman